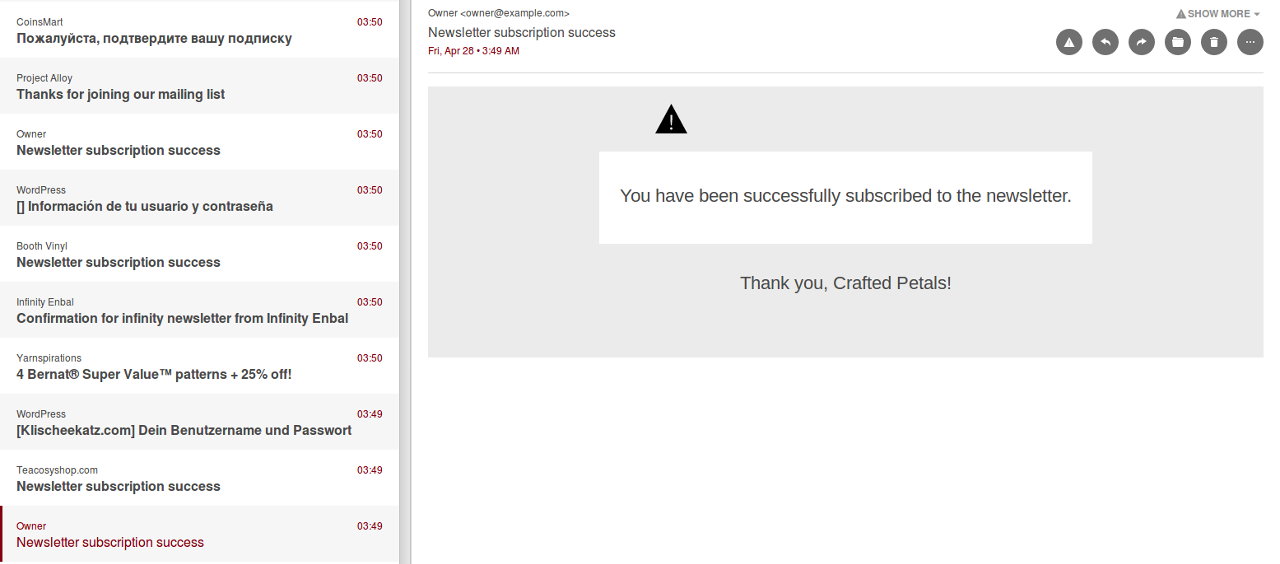
Email bomb hit Tutanota's contact email address with 500.000 newsletters
Newsletter email bombs are attacks on an email address that send thousands of newsletter sign-ups to a mailbox, rendering this mailbox useless. Email bombs are very easy to execute as all the attacker needs is a webcrawler and the targeted email address. Tutanota has now developed a fix against email bombs.
Now that we have implemented a fix, we want to apologize to our users, and in particular to businesses interested in Tutanota, who were contacting us during that time. It was impossible for us to find the legitimate mails among the hundreds of thousands of newsletter mails, so unfortunately we weren’t able to answer.
It took us several days to stop this attack, and the fact that about 30 new mails were popping up each minute did not make things easier. Now that we have fixed the issue, we are working hard on catching up on your mails.
No mail service offers protection against newsletter email bombs
The newsletter bomb is a known attack that has been going on for a while. Basically every known email address can be attacked with such a newsletter bomb. That’s also why journalists oftentimes fall victim to such attacks.
Security Blogger Brian Krebs has reported on email bombs when he was targeted himself (along with over 100 dot-gov (.gov) email inboxes) last year: “The emails came in at a rate of about one new message every 2-3 seconds. By the time I’d finished deleting and unsubscribing from the first page of requests, there would be another page or two of new newsletter-related emails. For most of the weekend until I got things under semi-control, my Gmail account was basically useless.”
As far as we are informed no mail provider has come up with a solution so far. Mail services can’t protect their users from this attack because they can’t put all newsletter services on a blacklist. It is impossible for the mail services to differentiate between legitimately signed up for newsletters and newsletters that were being signed up for illegitimately by an attacker.
Newsletter email bomb very easy to execute
The problem with the newsletter bomb is that it is so easy to execute. It can be targeted to every publicly known email address: The attacker simply uses a webcrawler that searches for webforms with input[type=email] fields. Then the bot automatically signs up a particular email address to thousands of newsletters on the entire internet.
As a consequence, the targeted mailbox becomes useless as people need to spend hours to delete these mails and to unsubscribe from these unwanted newsletters.
Tutanota is the first to offer protection from newsletter attacks
That’s why Tutanota’s internal fix turns the verification process of newsletter emails around: Instead of asking the recipient to verify that they really signed up for the newsletter in question, any email coming from a non-whitelisted domain (ie. unwanted newsletters) is at first moved to spam automatically.
How Tutanota’s protection works
Our approach to protect a mailbox from newsletter email bombs is a semi-automated whitelisting approach:
- We whitelisted important mail addresses and mail domains so that these legitimate emails would be sent to our inbox.
- We sent all other mails to the Spam folder. The sender is notified about this, if he can be authorized via SPF (to prevent backscatter). The notification contains a link that might be used by the sender to get whitelisted immediately and to move the mail to our inbox automatically. The original attackers are not able to click this link, as they never receive these responses.
- We batch-delete all Spam mails once a week.
This way we still receive important messages but do not have to manually filter through the mail flood.
DDoS attack against a personal mailbox
The newsletter bomb is like a DDoS attack against a personal mailbox because the user will be unable to work with this mailbox. The easiest solution for private users would probably be to sign up for a new mail address and inform all legitimate contacts about this move.
With Tutanota this will soon not be necessary anymore. We are still improving our protection method against newsletter attacks. In the future, we will be able to protect any Tutanota mailbox against these attacks by sending all newsletter sign-up mails to the spam folder (as described above). Protect your mailbox easily and sign up for our secure mail service right now!
Newsletter email bombs can’t hit Tutanota again
Looking back, these were some stressful days for our developers, but also for our users who had to wait for our replies longer than usual. But after all, we can now say that we are prepared for the future. Newsletter email bombs are no longer a threat to Tutanota.