US federal agencies required to adopt post-quantum security, private sector advised to follow
In an era of quantum computing "arms race", it is time to transition to quantum-safe systems.
PQ encryption in the U.S. National Cybersecurity Strategy
The Biden administration released the National Cybersecurity Strategy including a strategic objective 4.3, dealing with how to “prepare for our post-quantum future,” which states that
“we must prioritize and accelerate investments in widespread replacement of hardware, software, and services that can be easily compromised by quantum computers so that information is protected against future attacks.”
This follows bipartisan legislation adopted in December - and cited in the current strategy - encompassing post-quantum cybersecurity guidelines.
The Quantum Computing Cybersecurity Preparedness Act “aims to overcome the threat of near-future quantum computers defeating current cryptographic algorithms […] Once achieved, quantum computing will render digital data encrypted using current encryption techniques vulnerable to cyber threat actors.”
The new legislation encourages federal government agencies to adopt technologies resistant to quantum decryption attempts. The Office of Management and Budget is required to start implementing NIST-approved cryptographic algorithms to protect IT systems in the executive branch by July 5, 2023. Additionally, it is required to submit a report detailing the strategy and necessary funding to transition to quantum-safe systems by December 21, 2023.
A third provision of the bill requires the agency to coordinate with international standards organizations for post-quantum security.
The Cybersecurity Strategy also asks the private sector in the US to “follow the government’s model in preparing its own networks and systems for our post-quantum future.”
Why now?
Quantum computing is no longer a distant possibility, but already a reality. The Riken research institute in Japan has announced it will make the country’s first domestically built quantum computer available online for several businesses and academic institutions, by the end of this month. Riken plans to connect this quantum computer prototype to the world’s second-fastest supercomputer, Fugaku, by 2025, in order to expand its real-world use cases, including research related to materials and pharmaceuticals.
This is not an isolated development, but part of what looks like a quantum computing “arms race”. According to Japan’s Science and Technology Agency, over the past three decades China has registered the most patents worldwide for quantum computing, approximately 2,700, followed by the U.S. with roughly 2,200 and Japan with 885.
It’s clear that the world is on the verge of a technological revolution with the emergence of quantum computers, which promises unprecedented processing power and the ability to solve complex problems that classical computers cannot.
While this is exciting, it will also pose a threat to current encryption protocols, which could be easily broken by quantum computers, leaving sensitive information exposed to attackers. This is why the U.S. National Cybersecurity Strategy is calling for the transition to post-quantum cryptography, which uses algorithms that are resistant to attacks by quantum computers. The strategy recognizes the need to prepare for the future and ensure that encryption protocols remain secure in the face of evolving threats.
While the possibility of a quantum computer successfully breaking current end-to-end encryption protocols is not expected to become a reality in the immediate future, it is important to work on preventing this type of threat as soon as possible, because efficient solutions take time to develop.
Tutanota is breaking new ground with PQ encryption for email
Last year in July, as a result of the third round of the NIST PQC Standardization Process, NIST identified four candidate algorithms for standardization. They recommended two primary algorithms to be implemented for most use cases: CRYSTALS-KYBER (key-establishment) and CRYSTALS-Dilithium (digital signatures).
At that time, Tutanota had already identified these same two algorithms as the best choice for quantum resistant email encryption and had implemented them in a working protoype.
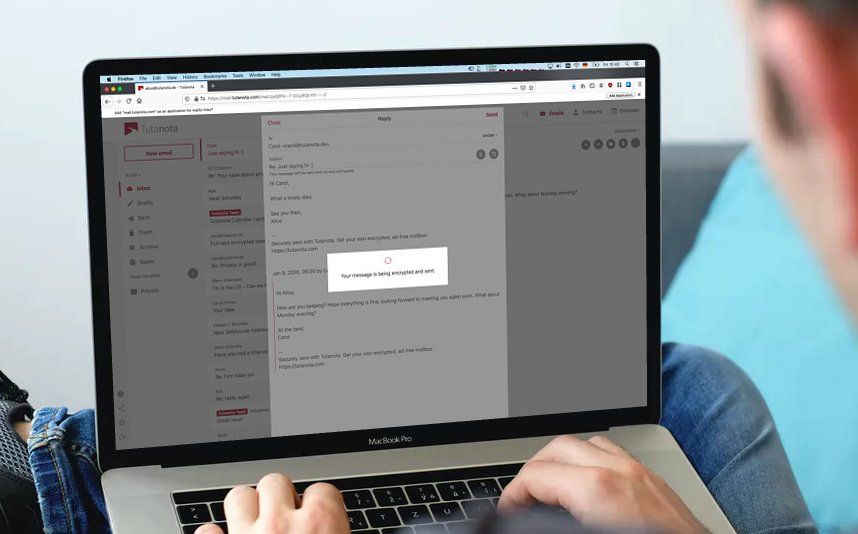
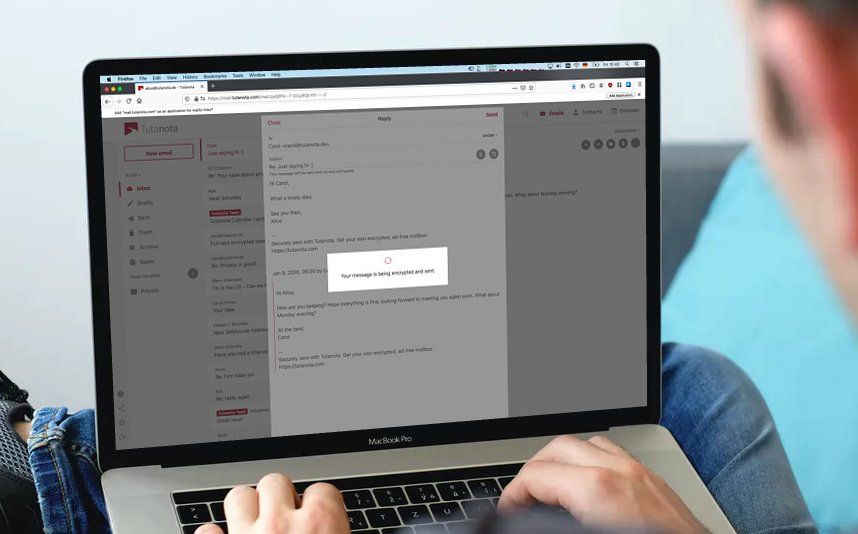
We had been working in partnership with the L3S research institution of Leibniz University Hanover on a research project, PQMail, for which we evaluated all NIST algorithms from Round Two in regards to security, a low resource impact and a fast performance before settling on CRYSTALS-Kyber and CRYSTALS-Dilithium.
“Our protocol was designed to theoretically be able to work with any of the candidates that NIST had identified in Round Two, but our performance tests showed that the CRYSTALS family would provide the best experience for our users”, explained Vitor Sakaguti, member of the PQMail research team. “CRYSTALS-Kyber and CRYSTALS-Dilithium had the lowest resource impact (key and signature sizes) and were the fastest, while still providing the security levels we were targeting, that is, at least as secure as 128 bit security with current algorithms on classical computers.”
The project is ongoing and we expect to have the first version of a PQ Tutanota email client made available to all our users in the near future. Additionally, our post-quantum prototype is already able to support Perfect Forward Secrecy and this feature will also be implemented in the Tutanota clients within the span of a few months after the post-quantum release.
While the transition to post-quantum cryptography will be challenging, it is necessary to ensure the security of sensitive information in the future. These efforts are critical because traditional encryption protocols will no longer be secure once quantum computers become widely available. Attackers will be able to exploit the vulnerabilities of existing encryption methods to access sensitive information, such as financial transactions, personal data, and confidential communications, putting everyone at risk, from private individuals, to businesses, to governmental institutions.
As Tutanota co-founder Arne Moehle states, “in the future, to protect data against growing threats we need innovative approaches to encryption, for instance post-quantum cryptography, quantum key distribution, forward secrecy or homomorphic encryption.All of these will be important to keep data safe from preying eyes while technology advances.”
Unlike PGP implementations, the encryption protocols that we already use enable us to easily upgrade to new algorithms and add support for Perfect Forward Secrecy.
“As the migration to new algorithms is done automatically in Tutanota, users will not have to do anything. Once the new protocol is implemented, all the data stored in Tutanota – that is emails, contacts, and calendars – will automatically be encrypted with the new algorithms”, our co-founder Matthias Pfau explained. “This will safeguard all data of millions of users against attacks from quantum computers.”
By adopting post-quantum encryption, we are taking a proactive approach to ensuring that our users’ data remains secure in the face of future threats. Our investment in this project enables us to deliver on the promise made to our users - to build the most secure email service in the world. We’re committed to staying ahead of the curve when it comes to encryption technology and making sure that our users’ privacy is not compromised by evolving threats.