Worst US hack in history: Chinese can monitor all your calls and emails.
Salt Typhoon has infiltrated major telecom networks, proving backdoors to encryption are a catastrophic risk.
The United States is grappling with what is being described as the worst telecommunications hack in US history, attributed to state-sponsored Chinese attackers Salt Typhoon.
This ongoing cyberattack has deeply infiltrated the networks of major U.S. telecom providers, including AT&T, Verizon, and T-Mobile. The sheer depth of the breach has made it exceptionally challenging to eradicate the attackers from the compromised systems.
”A catastrophic breach”
Mark Warner, the Democratic chairman of the Senate Intelligence Committee, described the attack as “the largest telecommunications hack in U.S. history – by far.”
Speaking to The Washington Post, Warner highlighted that this intrusion dwarfs previous cyberattacks like those on Colonial Pipeline or SolarWinds. He noted that removing the attackers would require replacing thousands, if not tens of thousands, of outdated devices such as switches and routers – a massive logistical and financial challenge. Because of this, the Chinese attackers are still able to monitor communications.
The attack, attributed to the groups known as “Salt Typhoon,” “GhostEmperor,” or “FamousSparrow,” was initially detected over a month ago but is believed to have started more than a year earlier. Its primary goal appears to be intelligence gathering.
High-stakes targets
The attackers managed to intercept real-time phone conversations, including those of high-profile individuals such as Donald Trump, J.D. Vance, and staff members of current Vice President Kamala Harris. Although there is no direct evidence linking the breach to the 2024 U.S. presidential election, the implications are severe. Warner revealed that the FBI has so far identified fewer than 150 individuals as victims, but those individuals have been in contact with “millions,” suggesting the scale of the breach could grow dramatically.
Moreover, the attackers accessed systems used by U.S. law enforcement agencies for surveillance. This means they could potentially learn who is under investigation, although no evidence has yet surfaced that they accessed the recorded surveillance data.
Encryption: first line of defense
According to cybersecurity experts, the attackers deployed sophisticated tools, including a Windows kernel rootkit named Demodex, to gain and maintain access to these networks. Their infiltration allowed them not only to eavesdrop on conversations but also to extract general internet traffic and other sensitive data. “Given the state of detection, it is impossible for us to predict when we will fully drive the attackers out of these networks,” Jeff Greene, Executive Assistant Director for Cybersecurity at CISA, said at a press briefing.
In a warning issued this week, U.S. officials admitted they have been unable to fully expel Chinese state-sponsored hackers from the networks of major telecommunications and internet service providers. As the breach continues to compromise sensitive communications, officials urged concerned users to switch to encrypted messaging and voice-calling services.
”Ensure that traffic is end-to-end encrypted to the maximum extent possible.”
The inability to secure critical telecommunications infrastructure leaves individuals and businesses vulnerable to surveillance. Unencrypted communications can be intercepted and analyzed in real-time, posing risks to privacy, security, and even national safety.
Encrypted services, such as Signal or Tuta Mail, offer a critical layer of protection by ensuring that messages and calls are protected with quantum-safe end-to-end encryption and accessible only to the intended recipients. Unlike traditional telecom systems, these services use end-to-end encryption, making it impossible for attackers - or even the service providers themselves - to access the content of your conversations.
The breach has no clear resolution timeline, and while efforts to secure affected networks continue, individuals must take immediate action to protect themselves.
Switching to encrypted communication platforms is one of the most effective ways to safeguard your privacy.
Proof that backdoors must never be
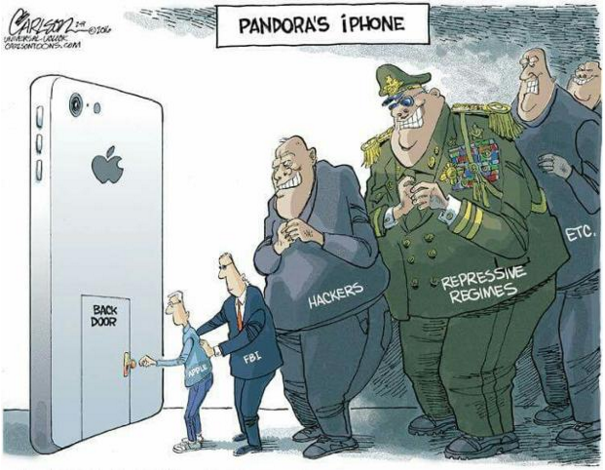
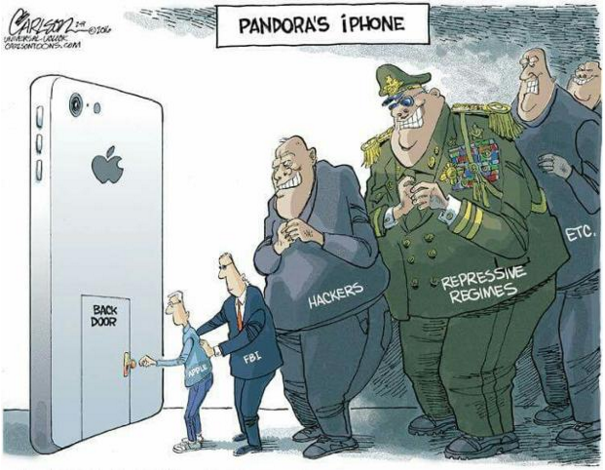
The ongoing Chinese hack of major U.S. telecom providers has exposed a sobering reality: attackers have gained access to systems used by U.S. law enforcement for surveillance. This breach underscores why backdoors to encryption must never be allowed, as they would inevitably create vulnerabilities that could be exploited by malicious actors, including foreign state attackers.
A “backdoor” in encryption is a deliberate vulnerability created to allow government agencies or other entities to bypass encryption and access data. Proponents argue that backdoors are necessary for national security and law enforcement to track criminals and terrorists. However, the Chinese hack demonstrates that backdoors create more problems than they solve.
When backdoors exist, they are not exclusive to those they are meant to serve. A backdoor is essentially a master key, and if it exists, someone - be it a state-sponsored attacker, a rogue insider, or a cybercriminal - will find a way to exploit it.
End-to-end encryption - without any backdoors - ensures that only the sender and receiver can access the data. This is the only way to guarantee privacy and security in the digital age. It protects individuals from attackers, corporations from industrial espionage, and even governments from adversarial nations.
Lessons from the Chinese hack on US officials
The Chinese hack highlights a painful truth. Attackers are relentless, sophisticated, and capable of exploiting any weakness. Introducing backdoors to encryption would hand them the keys to all of our data. Instead of increasing security, it would destroy the very protections we rely on.
In a world where cyberattacks are growing in scope and complexity, strong, unbroken encryption is an absolute necessity - one that everybody’s security depends on.
The only way to protect our communications, our data, and our free democracies is to resist calls for backdoors and uphold end-to-end encryption for everyone.