What is U2F used for and what are the benefits?
A U2F security key is important to secure your authentication process. These U2F security keys protect your account from malicious take-over, including pishing attacks. This guide helps you to understand what a U2F security key is and why we at Tuta recommend using one. This helps you to never lose access to your online identity!
What exactly is U2F and what is it used for?
tl;dr: U2F is important as it is the most secure option to protect your account credentials. Therefore, activate it wherever possible.
In fact, U2F is so important that every email service should support it.
The reason is simple: Your email account is the gate to your online identity. Think about it: services like Amazon, X, PayPal (just to name a few) and others are all linked to your email account. Even if you use strong psswords for these services, they can be easily reset if a hostile attacker has gained acces to your mailbox.
That’s what (FIDO) U2F security keys protect you from. If activated on your email account, for instance in Tuta, it will be close to impossible for malicious attackers to take over your mailbox.
What is U2F (Universal 2nd Factor)? - Definition
U2F is an open authentication standard that uses one key for multiple services. It simplifies and elevates the security provided by 2FA (two-factor authentication) as no drivers or client software is needed.
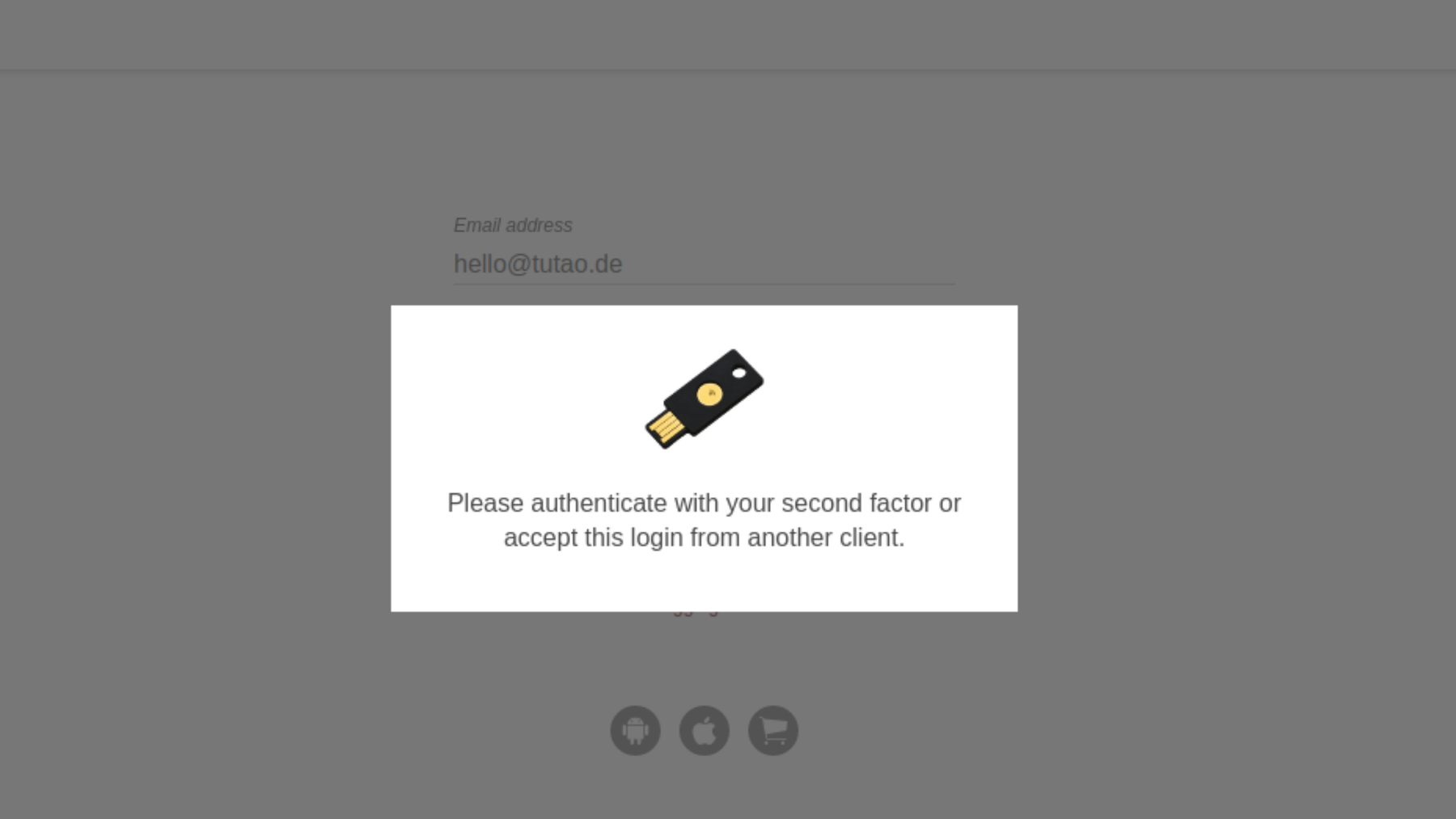
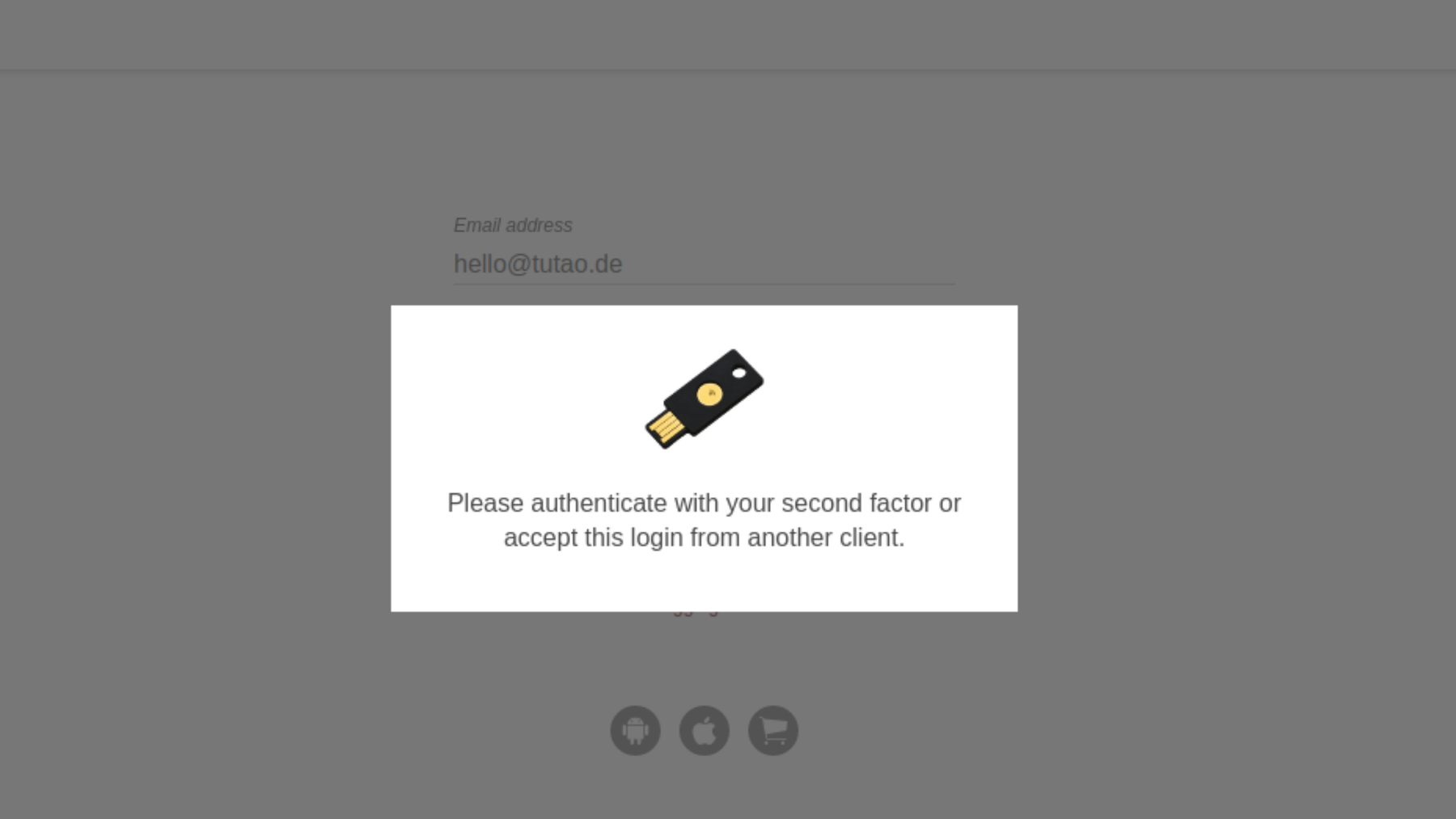
Universal second factor authentication refers to a separate device that holds a secret, extra key required to log into your digital account(s). Instead of entering a certain code (OTP), you just need to plug in a device as second factor.
**Further reading: 4 ways to protect your digital identity today.
U2F security keys vs. 2FA authentication
U2F keys are not the same as 2FA: 2FA is two-factor authentication that includes all methods for the second factor (for example SMS, TOTP, U2F and more). U2F security keys offer just one option on how to set up two-factor authentication - though the most secure one!
What are the benefits of using a U2F security key?
- Fast Authentication: Decrease time to authenticate
- Strong Security: No account takeovers when deployed fully
- Multiple Choices: Access to nearly 1,000 apps and services
What are the disadvantages?
There is one significant disadvantage of U2F solutions in comparison to TOTP (which uses a shared secret): For U2F there is no option to back up recovery codes of shared secrets.
If a hardware security key is lost, it will become impossible to login to the services and apps that were originally secured with this hardware security key. Thus, most services offer a way to reset the login credentials to regain access.
For instance, Tuta offers a recovery code that must be entered along with the correct password to reset (in this case: remove) a lost U2F security key. Additionally, it is possible in Tuta to register multiple U2F security keys. If one gets lost, users can still login with one of the other registered U2F security keys.
Is U2F really necessary for everyone?
In general, we at Tuta recommend everyone to secure their Tuta login credentials with a U2F security key.
At Tuta we recommend everyone to use a second factor like a Yubikey.
U2F authentication
U2F – second-factor authentication with a hardware security key – is the most secure way to protect your online accounts from malicious attacks like credential stuffing. It is also more secure than second-factor authentication via OTP or TOTP, so-called One-Time Passwords or Time-based One-Time Passwords. These are generated codes that are only valid for a short period of time. Therefore, we at Tuta highly recommend to activate a hardware key to protect your encrypted mailbox.
How do U2F security keys protect against phishing?
U2F security keys harden your login credentials, which make sure no one can take over your accounts - not even after a successful phishing attack.
In nowadays digitalized world where everything happens online, phishing emails are becoming more and more sophisticated. This means that there also is an increased risk of falling for such attacks. The sender of the phishing email usually tries to make you click a link where you are supposed to enter your password. Should this happen, the attacker can then easily steal your password and take over your account.
However, if a second factor like U2F has been activated on your account, the password will be useless to the attacker and your account will be safe.
On top of that, a U2F-enabled user login is bound to the origin; this means that only the real site can authenticate with the key (second factor). The authentication will fail on any fake phishing site even if the user was fooled into thinking it was real.
Why should you activate a second factor authentication (2FA)?
- A U2F security key increases the protection of your accounts (such as email, drive or social media accounts).
- A U2F security key is the most secure version of two-factor authentication.
- A U2F device creates a cryptographic key to unlock your account.
- Phishing attacks become close to impossible with a U2F security key.
How do U2F security keys work?
For the user, U2F security keys are really simple. You can activate the same U2F security key on all your accounts, such as Tuta, Amazon, or X. When you login, you enter your user name and password, and then you simply need to stick the USB-like hardware key into your device and tap it to finish the authentication process.
On a technical side, the process is much more complex. The Fido Alliance explains the process as follows:
“The U2F device and protocol need to guarantee user privacy and security. At the core of the protocol, the U2F device has a capability (ideally, embodied in a secure element) which mints an origin-specific public/private key pair. The U2F device gives the public key and a Key Handle to the origin online service or website during the user registration step.”
“Later, when the user performs an authentication, the origin online service or website sends the Key Handle back to the U2F device via the browser. The U2F device uses the Key Handle to identify the user’s private key, and creates a signature which is sent back to the origin to verify the presence of the U2F device. Thus, the Key Handle is simply an identifier of a particular key on the U2F device.”
“The key pair created by the U2F device during registration is origin specific. During registration, the browser sends the U2F device a hash of the origin (combination of protocol, hostname and port). The U2F device returns a public key and a Key Handle. Very importantly, the U2F device encodes the requesting origin into the Key Handle.”
“Later, when the user attempts to authenticate, the server sends the user’s Key Handle back to the browser. The browser sends this Key Handle and the hash of the origin which is requesting the authentication. The U2F device ensures that it had issued this Key Handle to that particular origin hash before performing any signing operation. If there is a mismatch no signature is returned. This origin check ensures that the public keys and Key Handles issued by a U2F device to a particular online service or website cannot be exercised by a different online service or website (i.e., a site with a different name on a valid SSL certificate). This is a critical privacy property - assuming the browser is working as it should, a site can verify identity strongly with a user’s U2F device only with a key which has been issued to that particular site by that particular U2F device. If this origin check was not present, a public key and Key Handle issued by a U2F device could be used as a ‘supercookie’ which allows multiple colluding sites to strongly verify and correlate a particular user’s identity.”
”The user is able to use the same device across multiple sites on the web — it thus serves as the user’s physical web keychain with multiple (virtual) keys to various sites provisioned from one physical device. Using the open U2F standard, any origin will be able to use any browser (or OS) which has U2F support to talk to any U2F compliant device presented by the user to enable strong authentication.“
History
Universal second Factor (U2F) is an open standard that strengthens and simplifies two-factor authentication (2FA) using specialized Universal Serial Bus (USB) or near-field communication (NFC) devices. It is succeeded by the FIDO2 Project, which includes the W3C Web Authentication (WebAuthn) standard and the FIDO Alliance’s Client to Authenticator Protocol 2 (CTAP2).
While initially developed by Google and Yubico, with contribution from NXP Semiconductors, the standard is now hosted by the FIDO Alliance alone.
You will find a list of all services that are supporting U2F security keys here.
Goal: Strong Authentication and Privacy for the web
The U2F eco-system is designed to provide strong two-factor authentication (2FA) for users on the web while preserving the user’s privacy.
The user carries a ‘U2F device’ as a second factor that logs them into their online accounts. This way, these accounts can be kept secure, especially from phishing attacks.
U2F hardware security keys are a great achievement as these make sure that people and their online accounts are kept secure on the web.
Comparison of different options for two-factor authentication (2FA)
Security device: U2F security keys
- Most secure option
- Private key is stored locally on U2F device
- Guarantees protection against man-in-the-middle attacks (MITM) and phishing
- Requires a hardware device
- No manual entry required
Authenticator app: TOTP
- An app generates codes that are only valid for a short period of time (Google Authenticator, Authy, etc.)
- Manual entry required upon every login
- Requires no hardware device
- Does not protect the mobile device login because app on mobile device generates second factor
Authenticator app: HOTP
- An app generates codes that are valid until used
- Less common used nowadays, most authenticator apps (Google Authenticatorm Authy, etc.) use TOTP by default
- Codes need to be stored securely
- Manual entry required upon every login
- Requires no hardware device
- Does not protect the mobile device login because app on mobile device generates second factor
SMS code
- Code is sent via SMS
- Manual entry required upon every login
- Least secure option as SMS can be easily intercepted
- Requires no hardware device
- Does not protect the mobile device login because SMS on mobile device contains second factor